This article discusses setting up Git server on a self-hosted server, e.g. you can buy an AWS EC2 and have your own git environment or you can have your own local server. (http://git.example.com).
If cost is not an issue, there are multiple services like github.com(Pricing model is number of repository based) and bitbucket.com (Pricing model is based on number of users – up to 5 user it’s all free, you can create n number of repository).
Pros:
Cons:
Steps for how to install Git on Ubuntu 12.04 LTS server, for other version steps are same, but I have tested on this version.
Assuming you have Ubuntu server ready and you are connected using Terminal app in Mac or some SSH tool.
Step #1: Install Git, Apache
$ sudo apt-get install git apache2
Step #2: Create the “git” user/group.
$ sudo adduser git
Fill all required information it asks, make sure you remember password.
Step #3: Setup Client Machine to manage Git Repos
This command should have created 2 files “id_rsa” and “id_rsa.pub” under $HOME/.ssh directory.
PS: If you would like to manage repository from other PCs later, you may need to share this key with new machine, feel free to contact me in case of trouble , I will be happy to help.
Copy “id_rsa.pub” file to your remote Ubuntu server which we are setting up as Git Server.
KB: scp is command to copy file on remote server, this command will copy “id_rsa.pub” file from Client Machine to Remote server. Make sure this command is fired on Client Machine 🙂
Step #4: Setup Git Admin
Switch back from Terminal to remote server!
Move and Rename pub key file to proper location now and also set owner to git group and user.
$ sudo mv /tmp/id_rsa.pub /home/git/Git-Adm.pub
$ sudo chown git:git /home/git/Git-Adm.pub
Step #5: Login as git user
Login as git user now, $ su -l git
Step #6: Gitolite installation
Gitolite is a tool to manage Git repos.
#1: Checkout source from github.
$ git clone https://github.com/sitaramc/gitolite
#2: Create bin folder at /home/git
$ mkdir bin
#3: Install gitolite
$ cd gitolite/
$ ./install
$ cd ..
$ /home/git/gitolite/src/gitolite setup -pk Git-Adm.pub
$ exit
Exit is to logout from git user, now you should be in your root account.
Step #7: Create bin folder to your Web Root and set permission and owner
$ cd /var/www
$ sudo mkdir bin
$ install -d -m 0755 -o git -g git /var/www/bin
Step #9: Scripts for Gitolite
$ cd /var/www/bin
$ sudo vi gitolite-suexec-wrapper.sh
Paste below script:
#!/bin/bash
#
# Suexec wrapper for gitolite-shell
#
export GIT_PROJECT_ROOT=”/home/git/repositories”
export GITOLITE_HTTP_HOME=”/home/git”
exec ${GITOLITE_HTTP_HOME}/gitolite/src/gitolite-shell
Set Proper permission
$ chown -R git:git /var/www/bin
$ chmod 750 /var/www/bin/gitolite-suexec-wrapper.sh
$ chmod 755 /var/www/bin
Step #10: Modify “UMASK”
$ sudo vi /home/git/.gitolite.rc
Change UMASK,
From:
UMASK => 0077
To
UMASK => 0027
Step #11: Clone Gitolite Admin repo to Client Machine
PS: Switch to your Client Machine terminal
$ mkdir ~/git-repos
$ cd ~/git-repos
$ git clone git@ip-address-of-git-server:gitolite-admin.git
Step #12: Adding new users and repos
Get pubkeys for your users
For example users “jaym” and “zaidp”.
Let’s create keys for “jaym” and “zaidp”
Make sure you create without passphrase
$ ssh-keygen -t rsa -C “Creating jaym keys” -f “jaym”
$ ssh-keygen -t rsa -C “Creating zaidp keys” -f “zaidp”
PS: keys will be generated in the same directory you are now in, it won’t create in ~/.ssh folder as you have provided -f parameter in command
KB: this time we have used -f param to specify file name of keys, if we don’t provide -f it will generate with id_rsa name only.
$ cp jaym.pub zaidp.pub ~/git-repos/gitolite-admin/keydir
Let’s create repository now, we will creating 3 repos
$ cd ~/git-repos/gitolite-admin/
$ vi conf/gitolite.conf
Updated gitolite conf looks like below,
repo gitolite-admin
RW+ = Git-Adm
repo testing
RW+ = @all
repo foo
RW = jaym
R = zaidp
repo bar
R = jaym
RW = zaidp
repo foobar
RW = jaym
RW = zaidp
PS: R is for Read and W is for Write.
Push changes to server now,
$ git add keydir conf
$ git commit -m ‘added users jaym and zaidp and also created sample repos’
$ git push origin master
Output:
Counting objects: 4, done.
Delta compression using up to 8 threads.
Compressing objects: 100% (3/3), done.
Writing objects: 100% (4/4), 455 bytes | 0 bytes/s, done.
Total 4 (delta 0), reused 0 (delta 0)
remote: Initialized empty Git repository in /home/git/repositories/bar.git/
remote: Initialized empty Git repository in /home/git/repositories/foo.git/
remote: Initialized empty Git repository in /home/git/repositories/foobar.git/
To git@192.168.1.40:gitolite-admin.git
6a5ee66..d032149 master > master
Step #13: How Jay and Zaid will be able to use Git
Assuming both are using Mac systems
#1: Send jaym key file to Jay in his Mac
#2: Jay needs to copy that file in ~/.ssh folder.
#3: in same ~/.ssh folder you should be able to find config file, if you cannot find you can create new file named “config”, PS: no extension.
#4: Open config file in any text editor. i.e. textedit, brackets
#5: Paste below line and save & close file.
Host git-jaym
HostName
User git
IdentityFile ~/.ssh/jaym
IdentitiesOnly yes
Let’s checkout repo.
#6: Now open terminal app
$ mkdir ~/foo
$ cd ~/foo
$ git clone git@git-jaym:foo.git
Output:
Cloning into ‘foo’…
warning: You appear to have cloned an empty repository.
Checking connectivity… done.
So that’s it! Jay is successfully able to checkout foo repo, we can do the same for other repo and other users!
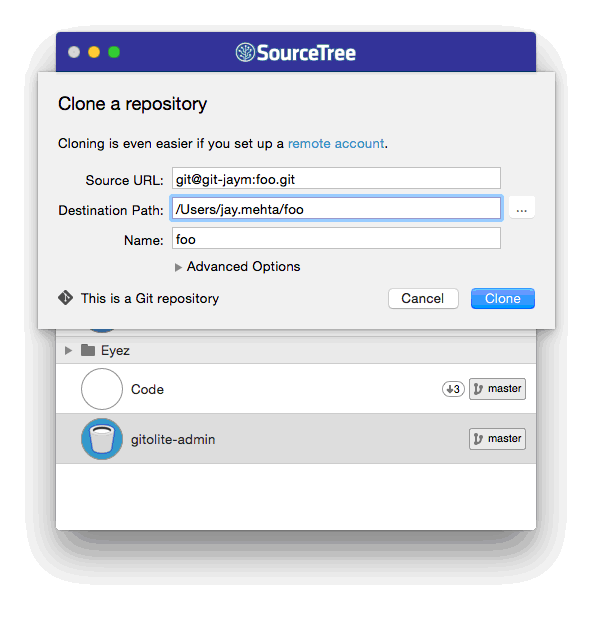
You can also use Sourcetree directly to checkout new Repo.
Share your findings with me and drop queries or troubles in comments, I will be happy to help! Happy coding!
Tell us a bit about your needs and our team will reach out to discuss how we can help.
Prefer mail? info@solutionanalysts.com